Curious about what Riskv is and how it affects your financial decisions? Let’s break it down with a simple explanation.
Definition
Riskv is a type of computer architecture that is based on the RISC (Reduced Instruction Set Computing) design philosophy. RISC architectures aim to simplify instruction sets and prioritize performance, making them popular for a wide range of computing applications.
One of the key features of Riskv is its open-source nature, allowing for greater flexibility and customization compared to proprietary architectures. This open standard has led to the development of a wide variety of Riskv-based products, from embedded systems to supercomputers.
By learning about Riskv, individuals can gain a deeper understanding of computer architecture and processor design, which can be valuable knowledge for those pursuing careers in software development or computer engineering. Taking Linux training courses that cover Riskv can provide a solid foundation for working with this innovative architecture.
Rationale and History
The **rationale** behind **Riskv** can be traced back to the need for an open-source, royalty-free architecture that promotes innovation and collaboration within the industry. Developed based on the **RISC** (Reduced Instruction Set Computing) principles, **Riskv** aims to provide a simple yet efficient design for processors, making it ideal for a wide range of applications.
Originally introduced by researchers at the University of California, Berkeley, **Riskv** has gained popularity due to its open standard and **32-bit** and **64-bit** computing capabilities. It has also found applications in areas such as embedded systems, personal computers, and even supercomputers, showcasing its versatility and efficiency.
With a strong emphasis on **open-source** architecture, **Riskv** has attracted a wide community of developers and enthusiasts who contribute to its continuous improvement and development. This collaborative approach has led to the creation of a robust ecosystem around **Riskv**, including various software tools and libraries that support its use in different environments.
Design and ISA Base
Designing an Instruction Set Architecture (ISA) Base is a crucial aspect of ***processor design***. It serves as the foundation for the ***processor’s microarchitecture*** and determines how instructions are executed. The ISA Base defines the ***operations*** and ***data types*** that a processor can handle, as well as the ***registers*** and ***memory addressing modes*** it supports.
When designing an ISA Base, ***efficiency*** and ***performance*** are key considerations. The goal is to create an ISA that allows for ***fast and efficient execution*** of instructions, while also enabling ***flexibility*** and ***scalability***. This involves optimizing the ISA for tasks such as ***parallel computing*** and ***vector processing***.
Understanding the intricacies of ISA Base design is essential for those looking to pursue a career in ***processor design*** or ***software development***. By mastering this aspect of computer architecture, individuals can contribute to the development of cutting-edge ***processors*** and ***computer systems***.
Profiles, Platforms, and Register Sets
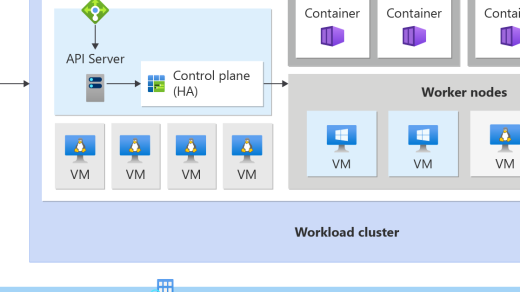
Profiles are sets of instructions tailored for specific applications or industries, allowing for optimized performance. Platforms refer to the hardware and software infrastructure supporting **RiskV** implementations. Register Sets are the storage locations within the **RiskV** processor for data manipulation.
Understanding these elements is crucial for developers looking to leverage the benefits of **RiskV** architecture in their projects. By mastering Profiles, Platforms, and Register Sets, individuals can harness the power of **RiskV** for efficient and high-performance computing solutions.
With **RiskV**’s open-source architecture and robust capabilities, learning about Profiles, Platforms, and Register Sets can pave the way for innovative and cutting-edge developments in the field of computing.
Memory Access and Immediates
When a program needs to retrieve or store data, it accesses memory through memory access instructions. These instructions specify the location in memory where the data is stored or retrieved.
Immediates, on the other hand, are values that are part of the instruction itself, rather than being stored in memory. They are used for operations that require immediate values, such as adding a constant to a register.
Understanding how memory access and immediates work in RISC-V is essential for writing efficient and effective programs. By mastering these concepts, developers can optimize their code for performance and reduce the chances of errors.
In the world of Linux training, a solid grasp of memory access and immediates in the RISC-V architecture can set you apart as a skilled and knowledgeable developer. Stay ahead of the curve by delving into this fundamental aspect of computer architecture.
Subroutine Calls, Jumps, and Branches
When a subroutine is called, the program jumps to a specific memory address to execute a set of instructions before returning to the main program. **Jumps** are used to change the program counter to a different location in memory, while **branches** are conditional jumps based on specific conditions.
Understanding how subroutine calls, jumps, and branches work in **Riskv** architecture is crucial for developers looking to optimize their code for performance and efficiency. By mastering these concepts, programmers can leverage the full potential of **Riskv** processors and enhance the overall functionality of their applications.
Atomic Memory Operations and Compressed Subset

Atomic Memory Operations in RISC-V refer to operations that are guaranteed to be executed without interruption, ensuring data consistency in multi-core processor environments. These operations are crucial for maintaining the integrity of shared data between different cores.
The Compressed Subset in RISC-V reduces the size of instructions, allowing for more efficient code execution and lower memory usage. This subset is optional but widely supported, making it a popular choice for embedded systems and devices with limited resources.
By understanding and utilizing Atomic Memory Operations and the Compressed Subset in RISC-V, developers can optimize performance and resource usage in their applications. This knowledge is essential for anyone looking to work with RISC-V architecture and contribute to the growing ecosystem of open-source hardware.
Implementations and Development Tools
| Implementation | Development Tools |
|---|---|
| RISC-V GNU Compiler Toolchain | GNU Compiler Collection (GCC), GNU Binutils, Newlib, GDB, etc. |
| RISC-V LLVM Toolchain | LLVM compiler infrastructure, Clang, LLD, etc. |
| RISC-V QEMU | QEMU emulator for RISC-V architecture |
| RISC-V Spike | RISC-V ISA simulator |