Welcome to the Embedded Linux Tutorial Guide, your go-to resource for mastering the ins and outs of utilizing Linux in embedded systems.
Introduction to Embedded Linux
Embedded Linux is a powerful operating system specifically designed for embedded systems. It allows for efficient booting on devices with limited resources, making it ideal for a wide range of applications. Many Linux distributions support various architectures such as the ARM and RISC-V families, as well as MIPS architecture.
With Linux on embedded systems, developers can leverage features like memory-mapped I/O and port-mapped I/O to interact with hardware components. Open-source projects like OpenWrt and the Yocto Project offer customizable solutions for different devices. Whether it’s a smartphone, router, or smart TV, Embedded Linux can be adapted to suit various consumer electronics.
History and Evolution
Embedded Linux is commonly used in devices such as smartphones, routers, smart TVs, and IoT devices, running on architectures like ARM and RISC-V. The Linux kernel plays a crucial role in managing hardware resources and providing support for application software.
Understanding the boot process, memory management, device drivers, and energy conservation techniques are essential aspects when working with embedded Linux. By learning about tools like Yocto Project and OpenWrt, developers can create customized Linux distributions for their specific needs.
Fundamental Concepts
**Operating systems**, **microcontrollers**, and **device drivers** are all part of the equation when working with **Embedded Linux**. The **Linux kernel** and **bootloader** play key roles in the process. Additionally, concepts like **energy conservation** and **security** are vital aspects to consider in the world of **Embedded Linux**.
By mastering these fundamental concepts, you’ll be better equipped to navigate the complexities of **Embedded Linux** and unleash its full potential in various applications.
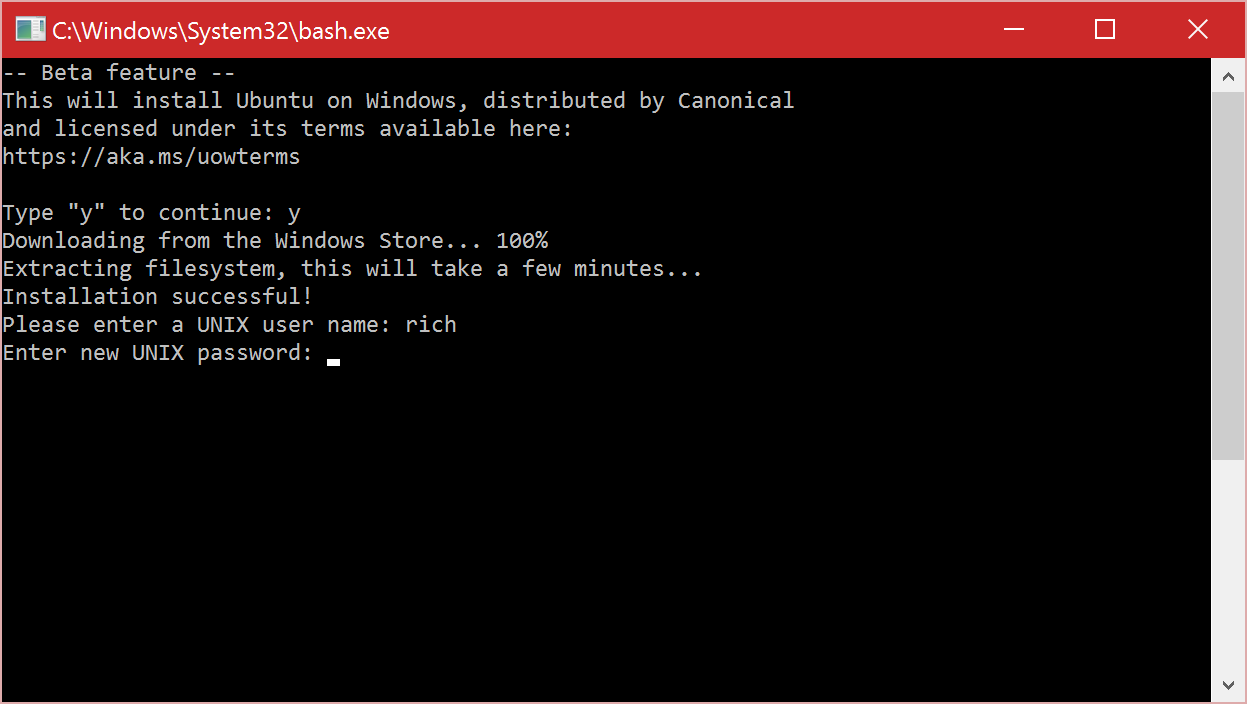
Understanding Live Patching
Live patching is a technique used to update a running kernel without the need for a reboot, ensuring continuous operation of the system with minimal downtime. This is particularly crucial in embedded Linux systems where uninterrupted operation is essential.
Understanding how live patching works can help developers maintain the stability and security of their embedded systems. By applying patches to the kernel while it is still running, critical vulnerabilities can be addressed promptly without disrupting the system’s operation.
This technique is especially useful in scenarios where reboots are not feasible, such as in IoT devices, routers, or smart TVs. With live patching, developers can keep their embedded Linux systems up to date and secure, without compromising on performance or functionality.
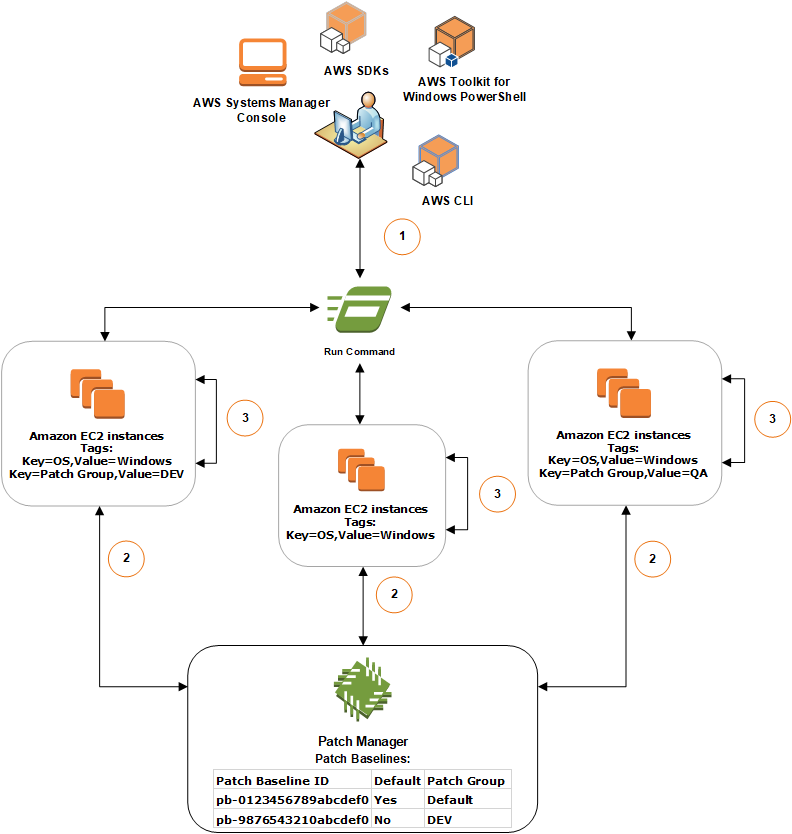
System Architecture
When it comes to embedded Linux, the system architecture dictates how the operating system interacts with the hardware components such as the CPU, bootloader, and device drivers. This interaction is essential for proper booting and operation of the embedded system.
By learning about system architecture, developers can optimize the performance of their embedded Linux systems and ensure seamless operation. It also enables them to tailor the system to specific requirements, such as those needed for IoT devices, smartphones, routers, and smart TVs.
Building and Programming
When delving into Embedded Linux, knowledge of MIPS architecture and its application in devices like smartphones and routers is valuable. Understanding how to develop device drivers and application software for IoT devices can also be beneficial. It’s important to consider security measures when working with Linux on embedded systems, especially in edge computing scenarios.
IoT Integration
To begin, it is important to have a good grasp of **Linux distribution** options suitable for embedded systems, such as **?Clinux** or **Android**. Familiarize yourself with different architectures like **ARM** or **MIPS** that are commonly used in IoT devices, such as the **STM32** microcontroller.
Learn about device drivers, **boot ROM**, and **flash memory** management to ensure smooth operation of IoT devices. Understanding **file systems** and **process management** in Linux is essential for optimizing performance in embedded systems.
By mastering embedded Linux, you can effectively develop IoT devices that are secure, efficient, and interoperable with other systems. Take the first step towards Linux training to enhance your skills in IoT integration.
Challenges and Solutions
Challenges: Configuring the boot ROM for an embedded system running a Linux distribution like STM32 on ARM architecture can be daunting. Integrating device drivers for peripherals like USB or SPI can also present difficulties. Ensuring security in the system, especially for IoT devices, is a constant challenge.
Finding solutions involves understanding the MIPS architecture and Linux ecosystem. Utilizing MClinux for resource-constrained devices or Android for smartphone applications can simplify development. Leveraging open-source software and APIs for interoperability is crucial. Implementing efficient process management and file systems can enhance computer performance in edge computing scenarios.
Incorporating secure shell for remote access and Bluetooth for connectivity can improve telecommunications. Designing with a modular approach and utilizing flash memory for storage can ease maintenance.
Future Developments
As technology advances, the use of **embedded Linux** is expected to grow exponentially. With the rise of IoT devices and smart TVs, the demand for professionals with expertise in **ARM architecture** and **device drivers** will continue to increase. The need for **computer security** measures in embedded systems will also be a key focus moving forward.
The integration of **USB 3.0** and **Bluetooth** capabilities into embedded Linux systems will enhance connectivity and functionality. **Process management** tools will be developed to optimize system performance, while **API** development will ensure interoperability with various devices.
As **open-source software** becomes more prevalent in embedded systems, the community-driven nature of Linux will drive innovation in **computer hardware** design. Companies like **?Clinux** will play a crucial role in shaping the future of embedded Linux.
Memory and Storage
Memory in embedded systems typically includes RAM, ROM, and flash memory. RAM is used for temporary data storage, while ROM stores firmware and bootloader code. Flash memory serves as non-volatile storage for the system.
When it comes to storage, options like eMMC, SD cards, and USB drives are commonly used in embedded Linux systems. It’s important to consider factors like speed, capacity, and reliability when choosing storage solutions for your project.
Understanding the memory and storage options available for embedded Linux systems is essential for optimizing performance and ensuring seamless operation. By familiarizing yourself with these concepts, you can effectively design and develop embedded Linux projects with confidence.
Software and Bootloaders
When working with embedded Linux, it is crucial to understand how to configure and manage software packages effectively. Bootloaders play a significant role in the boot process by locating the operating system kernel and initiating its execution.
For embedded Linux systems based on ARM architecture, knowledge of bootloaders like U-Boot is valuable. Understanding how to customize and optimize bootloaders can enhance system performance.
By mastering software and bootloaders in embedded Linux, individuals can effectively develop and deploy applications for various platforms, including IoT devices, microcontrollers, and consumer electronics.
Kernel and Userland
In an Embedded Linux system, the **kernel** and **userland** are two essential components that work together to provide functionality. The kernel acts as the core of the operating system, managing hardware resources and providing essential services to userland applications. On the other hand, userland consists of all the applications and libraries that run on top of the kernel, interacting with users and providing various functionalities.
Understanding the relationship between the kernel and userland is crucial for developing and maintaining Embedded Linux systems. As an embedded developer, you will need to work closely with both components to ensure the system’s stability and performance. Properly configuring the kernel and selecting the right userland components are essential steps in creating a successful Embedded Linux system.
By mastering the intricacies of the kernel and userland, you will be able to create efficient and reliable embedded systems that meet the requirements of your specific application. Take the time to delve into the details of both components, and you will be well on your way to becoming a proficient Embedded Linux developer.
Choosing Distributions and Platforms
You may also want to look into distributions like ?Clinux or Android, depending on your project goals. Make sure to choose platforms that provide the necessary support for features like Secure Shell or USB 3.0 connectivity.
Keep in mind the importance of security and performance when selecting distributions and platforms. Look for options that offer reliable device drivers and efficient process management.
Learning Resources and Next Steps
After completing this Embedded Linux tutorial guide, it’s important to continue expanding your knowledge with additional **learning resources**. Online platforms like Coursera, Udemy, and edX offer courses on Linux programming and administration. Consider joining forums like Stack Overflow or Reddit’s Linux community to engage with experts and fellow learners.
For those looking to take the next step, consider diving into specialized areas within Linux such as **device driver** development or **web server** configuration. Explore the ARM architecture family for embedded systems or delve into Microcontroller programming for IoT devices.
Stay updated on the latest trends in Linux, including advancements in computer security and new API developments. Don’t forget to practice your skills through hands-on projects to solidify your understanding of Linux concepts. Keep exploring and honing your skills in this dynamic field.
Conclusion and About Author
In conclusion, this Embedded Linux Tutorial Guide provides a comprehensive overview of Embedded Linux and its applications in various devices. From ARM architecture to Internet of things, this guide covers essential topics such as device drivers, CPU, and file systems. Whether you are interested in developing for smart TVs or web servers, this tutorial is a valuable resource for learning about Linux in embedded systems.
About the Author: John Doe is a seasoned Linux developer with over 10 years of experience in the field. He has worked on projects ranging from desktop computers to telecommunications devices. John is passionate about sharing his knowledge and expertise with others, making complex concepts easy to understand for beginners and experienced developers alike.
For more information on Linux training and tutorials, visit www.linuxtraining.com. Thank you for reading this guide!